Confidence through compliance
Cyber Security for Small and Medium Australian Businesses
Arotech’s Cyber Assurance services help your business establish strong foundations for governance, risk management, and compliance.
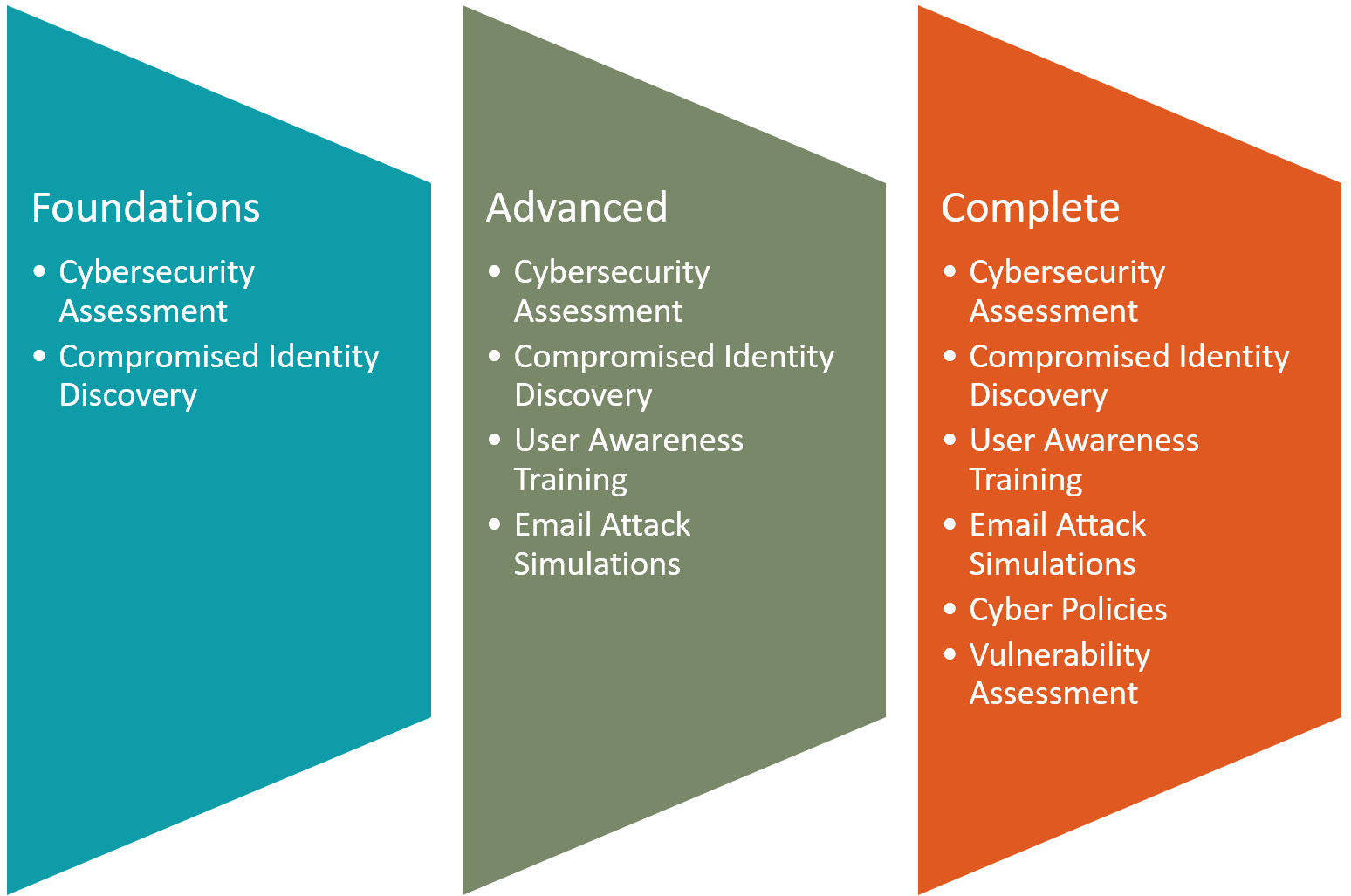
Small Business Packages
Arotech makes it easy for small businesses to start their cybersecurity journey with practical and affordable packages. Our solutions are designed specifically for growing Australian businesses that need real security without the complexity.
From securing your data and systems to meeting compliance requirements and responding to incidents, Arotech gives you the confidence that your business is protected from today’s cyber threats—so you can focus on running it.
Our Discovery packages will give you the insights on your risks so you can easily start your cybersecurity journey.
Cybersecurity Assessment
A comprehensive review of your current cybersecurity posture, this assessment identifies strengths, weaknesses, and gaps across your systems, networks, and processes. We look at how well your controls align with recognised security frameworks and everyday business risks, giving you a clear picture of where you stand.
You’ll receive practical, prioritised recommendations that fit your business size and resources — not generic advice. Whether you’re just starting to formalise your security practices or aiming to meet compliance standards, this assessment helps you make informed decisions to protect your business and build resilience.

Compromised Identity Discovery
Even the best-secured businesses can be exposed if employee or company credentials are leaked online. This service continuously monitors the dark web, criminal marketplaces, and data breach repositories to detect if your usernames, passwords, or domain details have been compromised.
When a threat is found, you’ll be alerted immediately with clear guidance on what to do next. Early discovery allows your business to reset credentials, strengthen access controls, and prevent unauthorised use of stolen information before damage occurs.

User Awareness Training
People are your first line of defence — and often the most targeted. Our interactive cybersecurity awareness training helps your team understand the latest threats, from phishing and social engineering to ransomware and credential theft. Training content is tailored for non-technical users and designed to be practical, engaging, and easy to apply in everyday work.
Your staff will learn to recognise suspicious emails, spot red flags, and follow best practices for data protection. Over time, this builds a security-minded culture across your business, reducing risk and turning employees into active defenders rather than potential vulnerabilities.
Email Attack Simulations
Phishing remains one of the most common ways cybercriminals target Australian businesses. Our email attack simulations safely replicate real-world phishing attempts to test how your staff respond under realistic conditions. The exercises measure awareness, identify risky behaviours, and highlight areas where additional support may be needed.
Following each campaign, you’ll receive detailed reports and targeted learning recommendations. By running regular simulations, your team becomes more confident in spotting and reporting malicious emails — helping to significantly lower the likelihood of a successful attack.

Cyber Policies
Strong cybersecurity policies are the foundation of consistent, secure behaviour across your business. We work with you to create or refine practical, easy-to-follow policies that set clear expectations for staff and management. These cover key areas such as password management, device use, remote work, data handling, and incident response.
Rather than using one-size-fits-all templates, our policies are tailored to your business operations, regulatory requirements, and risk profile. The result is a set of living documents that guide your team’s actions, support compliance, and strengthen your overall security posture.
Vulnerability Assessment
Cyber attackers look for weak points in your systems — and this service helps you find them first. Our vulnerability assessment scans your IT environment, applications, and networks to uncover outdated software, misconfigurations, and other security flaws that could be exploited.
Each finding is clearly prioritised based on actual business impact, helping you focus on what matters most. You’ll receive an actionable report with remediation steps, so your team can address vulnerabilities efficiently and maintain stronger protection against evolving threats.
Let us know which package you are interested in

